— Leadership
Building real systems for places software alone won't reach.
"I want my hardware to deserve its name. If a system is called HORUS, then it had better watch. If it is called MA'AT, it had better keep order. The naming is a promise to the people who depend on it."
Dr. Mohamed El-Hadedy is the founder and CEO of RecoIoT LLC and a tenured Associate Professor in the Department of Electrical & Computer Engineering at California State Polytechnic University, Pomona, where he directs the Reconfigurable Space Computing Lab (RSCL@CPP).
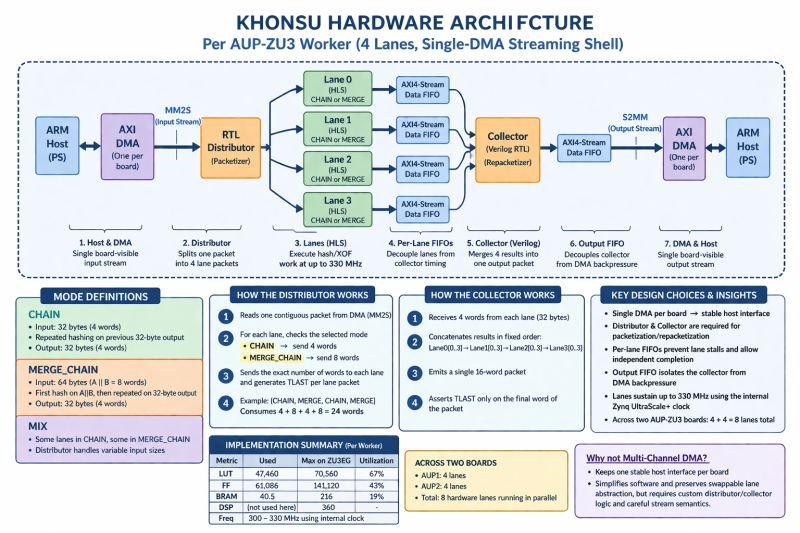
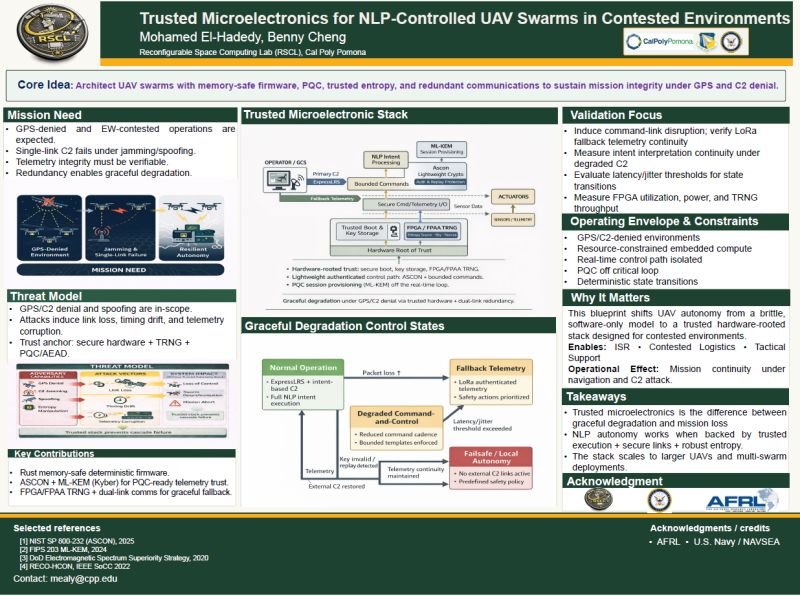
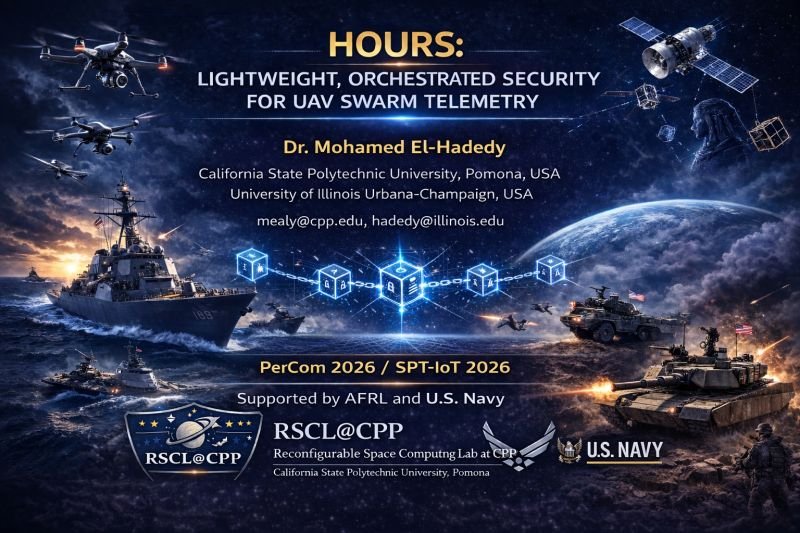
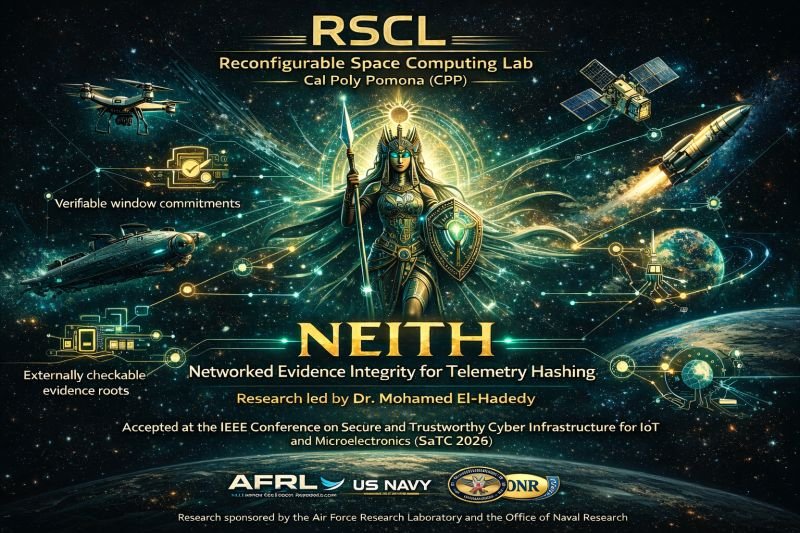
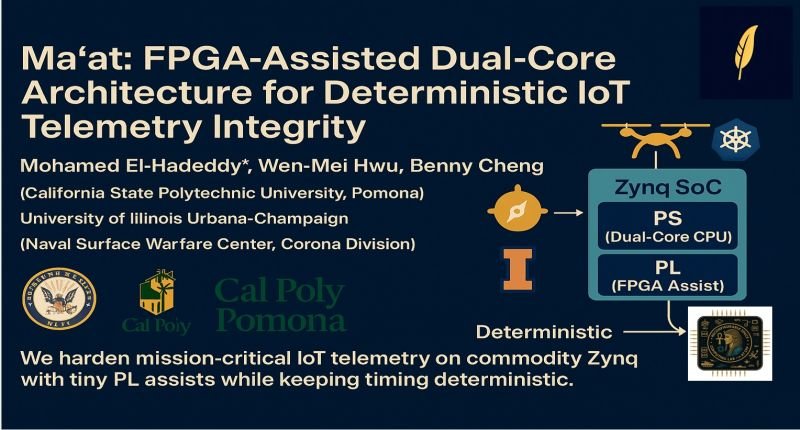
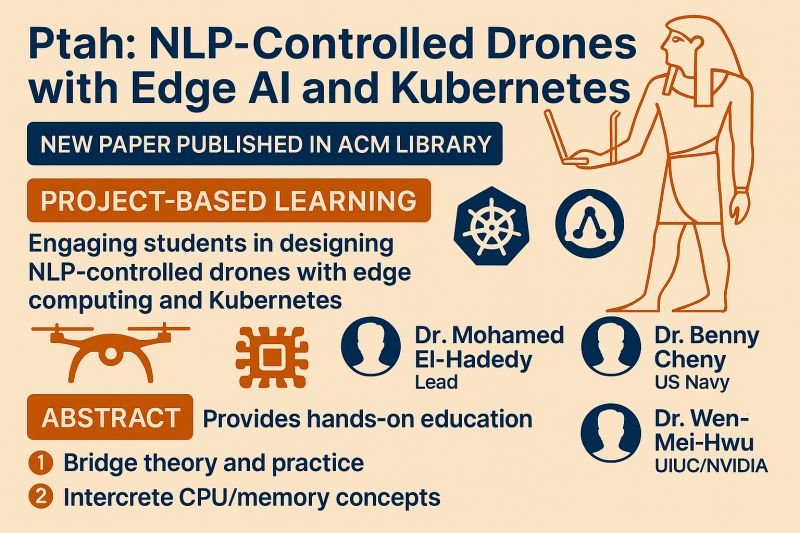
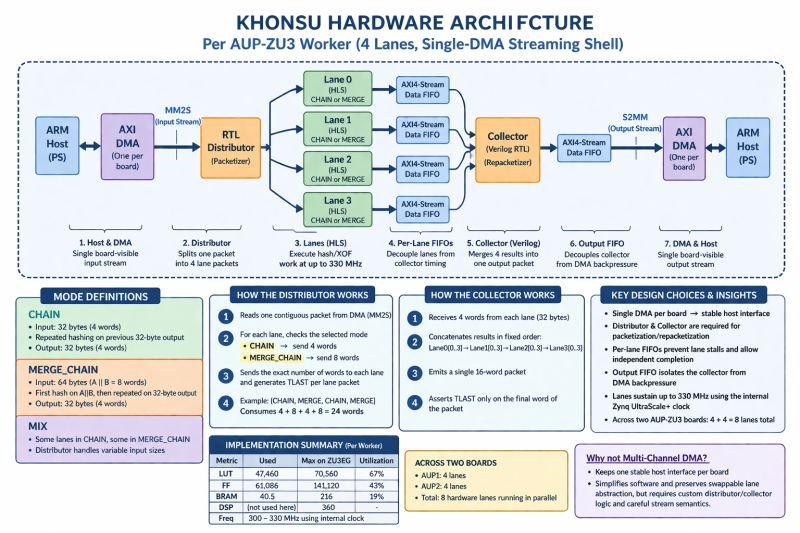
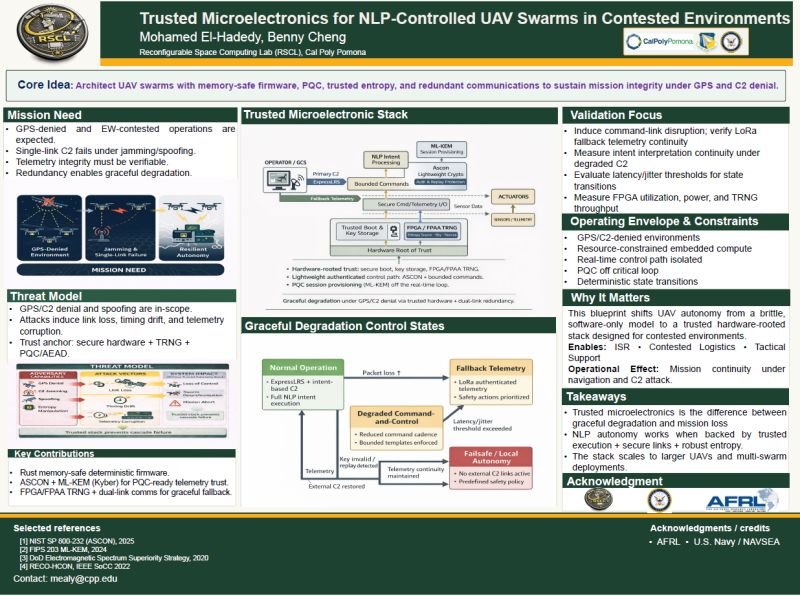
His research sits at the intersection of reconfigurable computing, embedded security, flight software, and mission-driven autonomy. What makes the work distinctive is that it does not stop at algorithms or simulations — it produces complete systems: FPGA and MPSoC prototypes, Kubernetes/edge testbeds, flight-software integrations, drone platforms, cryptographic services, sensor pipelines, and defense-relevant autonomy experiments. SEKHMET won Best Paper at NG-RES 2026/HiPEAC. HORUS turns unavoidable multirotor blade-pass noise into an acoustic side-channel for GPS- and RF-denied swarm awareness. MEHEN (under review at IEEE Space Computing) makes programmable fabric the backend of an F′ flight-software security component — not just hardware acceleration, but operationally visible security services integrated into real flight workflows. The core pattern across the work is capability creation, not incremental exercises.
Mohamed earned his Ph.D. from the Norwegian University of Science and Technology (NTNU), with a dissertation in cryptographic hardware co-design. He holds a Master's and Bachelor's in Electronics Engineering from Mansoura University, Egypt. Before academic research, from 2004 to 2008, he served as a Research Scientist at the Egyptian Nuclear Research Reactor — a foundation that informs his ongoing work on radiation-tolerant computing, single-event-effects (SEE), and trustworthy electronics for space.
After NTNU he joined Atmel Norway AS as a Senior Design Engineer, working on production microcontroller and FPGA silicon — the industry foundation that grounds every prototype RecoIoT builds today in real chip-design discipline. He then returned to academia as Postdoctoral Fellow at the University of Virginia and Senior Research Scientist at the University of Illinois Urbana-Champaign (UIUC) in collaboration with Wen-Mei Hwu. RecoIoT LLC was founded in 2017 to translate that research-and-industry lineage into deliverable hardware for U.S. defense and space programs.
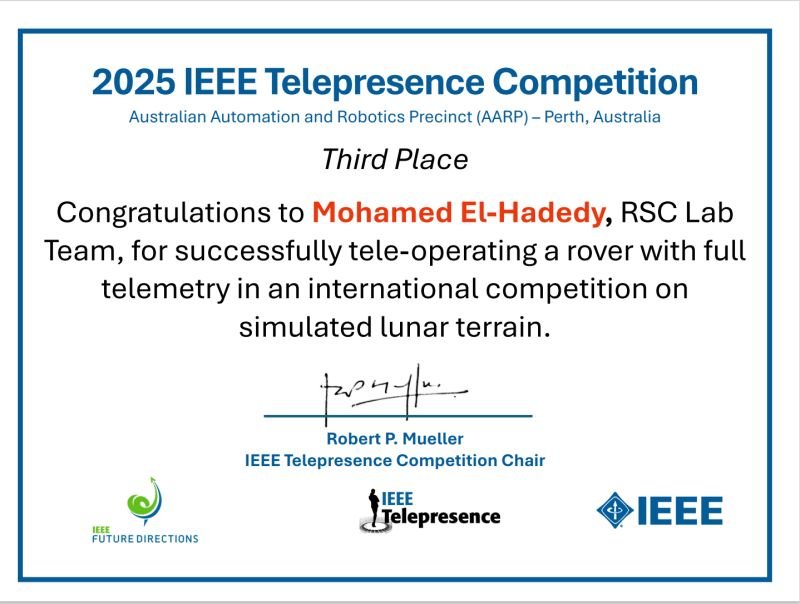
His record shows sustained, mission-aligned achievement: continuous federal support since 2017 from the Air Force Research Laboratory, U.S. Army Research Office, U.S. Navy NEEC and ONR, NSWC Corona, NASA, and Lawrence Berkeley National Lab — cumulative awards exceeding $5 million. Three issued U.S. patents in reconfigurable cryptographic processing and transposition-memory architecture, plus a fourth filed for a compliant inspection mechanism developed at Los Alamos National Laboratory. Three Best Paper Awards across NG-RES/HiPEAC 2026, RAW/IPDPS 2016, and SRC TECHCON 2016. Third Place at the 2025 IEEE Telepresence Competition in Perth, Australia. Invited talks at LBNL in 2024 and 2025. More than seventy peer-reviewed papers. Mentor of multiple NASA MINDS finalist and award-winning teams. Senior Member of both IEEE and ACM.
His operating thesis is straightforward: the strongest defense systems are not the ones with the most software, but the ones with the most verifiable silicon — hardware that can be reasoned about, audited, and trusted at the component level. RecoIoT is built around that belief.
Doctorate
Ph.D., NTNUNorwegian Univ. of Science & Technology
Foundation
M.Sc. & B.Sc.Mansoura University, Egypt
Early Career
Research ScientistEgyptian Nuclear Research Reactor · 2004–2008
Academic Home
Cal Poly PomonaTenured Associate Professor, ECE
Memberships
IEEE Senior MemberACM Senior Member
Patents Issued
3 U.S. Patents+1 filed (LANL)
Industry
Atmel Norway ASSenior Design Engineer
Mentorship
NASA MINDSMultiple finalist & award-winning teams